
News
Secure Email, a Myth?
It’s been a week since the last Lavabit court documents were filed and here I am, still trying to make sense of the whole charade. When I first heard of the case, I wondered how it is possible that law enforcement agents can rummage around unchecked, even when their investigations bring them past the proverbial doorsteps of regular people.
Such was the case this past June when the FBI demanded the “master keys” to secure-email provider Lavabit’s servers. The order was part of an investigation into the Internet correspondence of Edward Snowden: one of Lavabit’s customers.
“But wait,” you say, “doesn’t a ‘master key’ mean that they could then monitor data on all of Lavabit’s customers? Even the ones that hadn’t done anything wrong?” To which I respond, “Elementary, dear Watson.”
So in light of this fact, the obvious question is then: does secure email even exist?
End-to-end security: the key is having more than one.
In a conversation with Johns Hopkins University cryptography professor Matthew Green, Green said that the answer is yes. It does exist. But according to him, the name of the game is “end-to-end” security. In short, end-to-end security is a type of program where data is encrypted locally on a user’s device before it’s sent through the server to a recipient. The recipient then uses his or her own password to decrypt the message. This bars even the provider from being able to untangle the data in a way that’s readable.
Green, who has written about the subject in The New Yorker, says that the way the company’s servers revolved around SSL decryption, or essentially one set of master keys, was “the real problem with Lavabit.”
“The mail that came in was not encrypted using your password,” he said. “It was encrypted using SSL. And so anyone who got that SSL could be able to read all the data. And so it wasn’t a very good design from that perspective.”
But end-to-end security is not exactly a perfect science either. More geared toward text messaging and phone communications, there are only a few programs that use end-to end security technology with email. They usually come in the form of add-ons such as Pretty Good Privacy or Privacy Guard, where senders and recipients must use the same service.
However, Green says that at encryption software company Silent Circle, programmers are working to change that. In late Oct., the company announced that, with the help of Lavabit founder Ladar Levison, they would develop a new product called Dark Mail that integrates end-to-end protection with their email service.
Wait on technology. Not on Washington.
In a blizzard of political headway that some are now calling “the Snowden effect,” many lawmakers have announced their efforts to rally behind surveillance reform. One such effort is the USA FREEDOM ACT, a bill that has, since its introduction in late Oct., picked up 102 cosponsors from both parties. The bill calls for heightened regulation on surveillance activities, such as pen/trap procedures like the one that spelled doom for Lavabit’s a few months ago.
But Green says that it’s not enough, “forget about the government. Just imagine that the only people after you are criminals. You’re not going to be able to rely on laws to protect you from that kind of person.”
Furthermore, where the bill now sits in a congressional committee might just be its final resting place.
“I would love to see some kind of legal solution to all of this surveillance but I’m not sure that we [will] get something that we can really rely on. Ways that you can protect yourself and add privacy is to do it yourself and to do it through technology rather than hoping that the laws are going to be changed.”
However, that’s not to say that Green opposes the bill.
“I haven’t really looked at the legislation… but it sounds like a good idea,” he said.
—
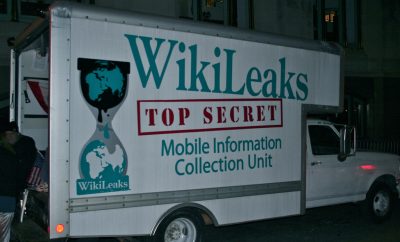
Featured image courtesy of [twitter.com/mattwi1s0n via Flickr]







Comments